Fake Discount Scams: How to Stay Safe While Shopping Online

Key Takeaways
- Rising Fraud Losses: Fake discount scams accounted for a significant share in total consumer fraud losses reported to the FTC, with online shopping ranking as the second most commonly reported fraud category.
- Sophisticated Deception Tactics: These scams rely on inflated "original" prices, urgency triggers like countdown timers, and cloned websites that closely mimic trusted retailers to trick shoppers into handing over payment details.
- AI-Driven Growth: Fake online store scams are now fueled by economic uncertainty and AI-generated storefronts.
- Widespread Impact: A survey found that roughly one in three U.S. adults has experienced an online shopping scam, including receiving counterfeit goods or never receiving a purchased item.
- Real-Time Protection Available: Guardio provides real-time protection against fake discount scams by blocking fraudulent shopping websites, flagging phishing links in emails and texts, and alerting users to data breaches tied to their accounts.
Fake discount scams are one of the most widespread forms of online fraud today. These scams disguise themselves as legitimate sales, flash deals, and promotional offers to lure shoppers into handing over payment details, personal information, or both. With AI-generated storefronts and sophisticated social media ad targeting, spotting a fake deal has become harder than ever.
So how do you stay safe while shopping online? It starts with understanding how these scams operate, recognizing the warning signs before you click, and using the right security tools to catch what manual checks might miss. This guide covers the mechanics behind fake discount scams, the red flags to watch for, what to do if you fall victim, and how platforms like Guardio provide real-time protection against fraudulent shopping sites across desktop and mobile.
{{component-cta-custom}}
What Are Fake Discount Scams?
Fake discount scams are fraudulent schemes designed to lure online shoppers with deals that appear too good to pass up. They typically involve counterfeit websites, social media ads, or promotional messages advertising steep price drops on popular products. The goal is not to deliver a bargain, but to steal payment information, personal data, or both.
These scams have grown rapidly alongside the expansion of online shopping. According to the FTC’s 2024 Consumer Sentinel report, consumers reported losing over $12.5 billion to fraud in 2024, a 25% increase from the previous year, and online shopping was the second most commonly reported fraud category. A Pew Research Center survey conducted in April 2025 reports that 36% of U.S. adults say they’ve bought an item online that turned out to be counterfeit or never arrived (and wasn’t refunded).
Fake Discount Scams vs. Legitimate Discounts
Telling the difference between a genuine sale and a fake discount scam is harder than it used to be. Scammers have become skilled at replicating the visual language of real promotions. The table below breaks down three common tactics used by scam operators and compares them directly against their legitimate counterparts.
How Fake Discount Scams Work
Fake discount scams follow a structured playbook. The specifics vary, but the underlying strategy remains consistent, which attracts shoppers with an irresistible offer, routes them to a controlled environment, and extracts value, whether that means payment information, login credentials, or personal data.
Social Media and SMS Distribution
Social media platforms and text messages are two of the most common delivery channels for fake discount scams. Scammers create ads or sponsored posts that appear in users’ feeds, often mimicking the look and tone of real brands. These ads typically feature deeply discounted products and direct users to fraudulent storefronts.
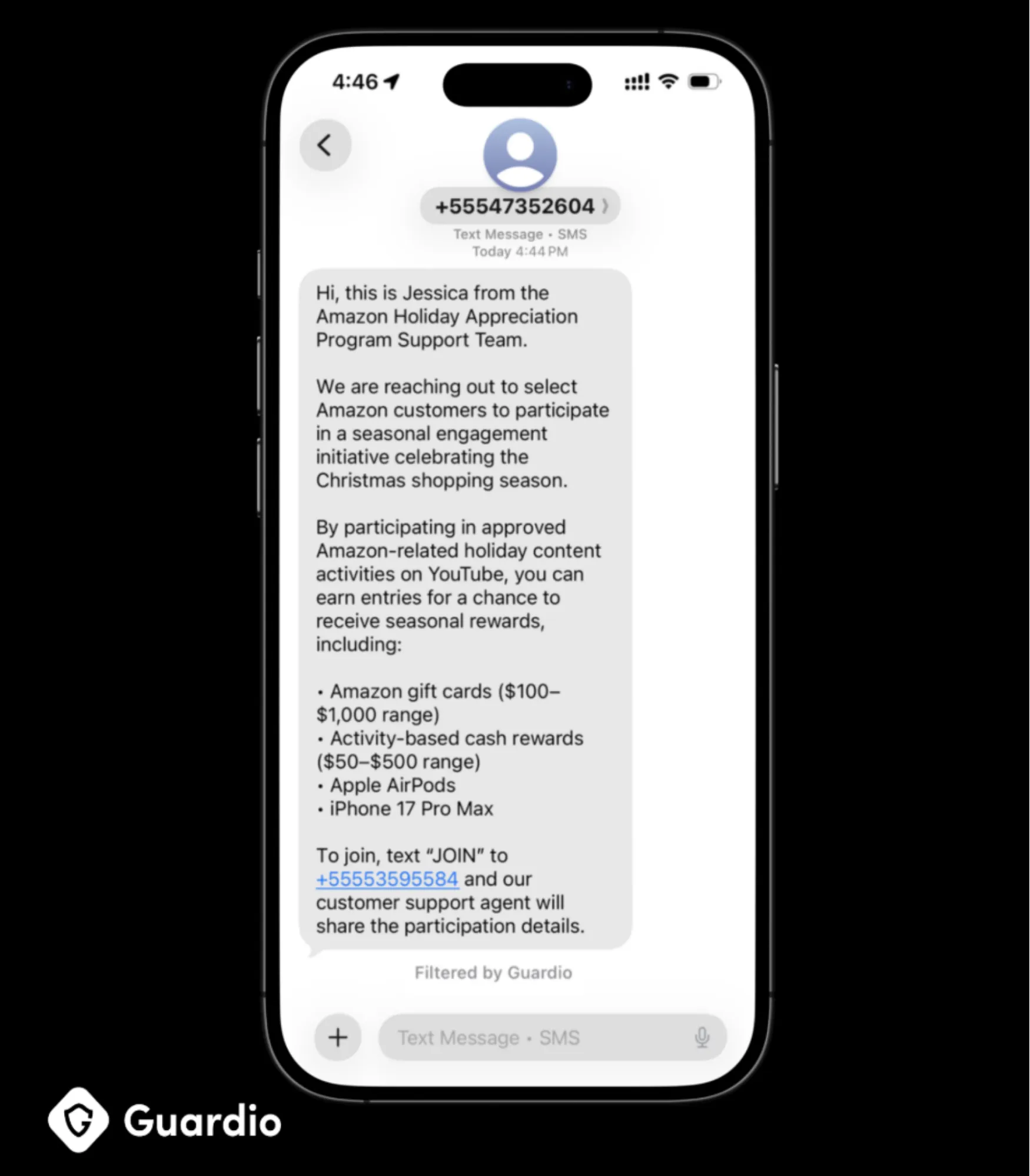
SMS-based scams follow a similar pattern where shoppers receive unsolicited texts promoting exclusive discounts or order confirmations for purchases they never made, each containing a link to a fake checkout or tracking page. The personal nature of text messages makes recipients more likely to engage, especially when the message appears to reference a recent transaction.
SEO Poisoning and Fake Sponsored Ads
Scammers also exploit search engine advertising to push fraudulent websites to the top of search results. By purchasing sponsored ad placements or manipulating SEO rankings, these operators ensure that their fake stores appear when shoppers search for popular products or discount codes. The result is a convincing search presence that can be difficult to distinguish from legitimate retailers, especially on mobile devices, where ad labels are less prominent.
A related tactic that has gained traction is what security researchers call "AI content poisoning." Scammers have learned to code and position fake websites in ways that appeal to AI search algorithms, increasing the chances that their fraudulent listings surface in AI-assisted shopping recommendations.
Lookalike Domains and Clone Websites
One of the most effective tactics used in fake discount scams involves creating websites that closely resemble legitimate retailers. These clone sites use the same logos, product images, fonts, and page layouts as the brands they impersonate. The domain names are designed to look authentic at first glance, often using slight variations such as extra words, hyphens, or alternative top-level domains.
Data Harvesting and Credential Theft
The end goal of most fake discount scams is not to sell a product. It is to collect data. When a shopper enters their name, address, email, phone number, and credit card information on a fraudulent checkout page, that data is captured and can be used for unauthorized charges, sold on dark web marketplaces, or leveraged in follow-up phishing attacks.
Some fake shopping sites go further by deploying malware that records keystrokes or installs browser extensions capable of monitoring future activity. Others use a "card declined" trick, where the site claims a payment method failed and asks for a second card, effectively capturing details from multiple accounts in a single transaction.
Why Fake Discount Scams Are So Dangerous
The consequences of falling for a fake discount scam extend well beyond the initial purchase. What may seem like a small transaction on a suspicious website can set off a chain of financial, personal, and security-related problems.
- Financial Loss and Unauthorized Charges: Victims may see charges for items that never arrive, or discover additional unauthorized transactions on their cards in the days and weeks following the scam.
- Identity Theft and Account Takeovers: The personal information collected during a fake discount scam, including names, addresses, phone numbers, email addresses, and payment details, can be repackaged and used for identity theft. If attackers use stolen credentials to access accounts, they can reset passwords, redirect shipments, or make purchases using stored payment methods.
- Long-Term Data Exposure Risks: Data collected through fake discount scams rarely stays with the original attacker. Stolen credentials and personal information are routinely sold in bulk on dark web forums, where they may be used by multiple threat actors over months or years.
Key Signs of Fake Discount Scams
Recognizing fake discount scams before you interact with them is the most effective form of protection. The warning signs below represent the most reliable indicators that a deal or store is not what it claims to be:
{{component-tips}}
What to Do If You Fall for a Fake Discount Scam
If you suspect that you have entered personal or payment information on a fraudulent shopping site, acting quickly can limit the damage. The steps below should be taken as soon as possible.
Contact Your Bank or Card Provider Immediately
Call the fraud department of your bank or credit card issuer and report the transaction. Request a temporary freeze on the affected card and ask about initiating a chargeback. If you paid with a debit card, the window for recovering funds is shorter, so speed matters. If the transaction involves a wire transfer or cryptocurrency, contact the payment platform immediately, though recovery in those cases is significantly more difficult.
Change Affected Account Passwords
If you used the same email and password combination on the scam site that you use elsewhere, change those credentials immediately. Prioritize email, banking, and any retail accounts tied to the same login. Use a unique, strong password for each account, and enable two-factor authentication wherever available. A password manager can simplify this process.
Monitor for Identity Fraud Signals
Watch for unusual activity across your accounts in the weeks following the incident. This includes unexpected login alerts, unfamiliar charges, new accounts opened in your name, or password reset emails you did not request. Consider placing a fraud alert or credit freeze with the three major credit bureaus (Equifax, Experian, and TransUnion) to prevent new accounts from being opened using your information. If you use Guardio, its breach and account-risk alerts can help surface exposure signals early, so you know which logins or settings to secure first.
Report the Scam to Relevant Authorities
File a report with the FTC at ReportFraud.ftc.gov, and submit a complaint to the Internet Crime Complaint Center (IC3). If the scam involves brand impersonation, notify the brand directly. Reporting helps law enforcement track patterns and can contribute to shutting down active scam networks.
Essential Security Layers for Safer Online Shopping
Individual vigilance is important, but relying solely on manual checks leaves gaps, especially as scam techniques become more sophisticated. The security layers below offer complementary forms of protection that reduce risk across different attack vectors.
- Strong Password Hygiene and Unique Credentials: Using the same password across multiple accounts creates a single point of failure. If one set of credentials is compromised through a fake discount scam, every account sharing that password becomes vulnerable. A unique password for each account, combined with a password manager, limits the blast radius of any single breach.
- Multi-Factor Authentication on Retail Accounts: Multi-factor authentication (MFA) adds a second verification step beyond your password. Even if a scammer captures your login credentials from a fake checkout page, they cannot access your account without the second factor. Enable MFA on all accounts that support it, especially email, banking, and frequently used shopping platforms.
- Real-Time Scam and Phishing Detection Tools: Security tools, such as Guardio, that evaluate websites in real-time provide a critical safety net. Unlike manual URL scanners, these tools work automatically as you browse, flagging phishing sites and fraudulent pages before you interact with them. This is especially important for fake discount scams, which often operate through short-lived domains that have not yet been added to static blocklists. It also gives you a fast go/no-go check on unfamiliar links, so you can confirm whether a URL is safe before you log in, enter payment details, or share personal info.
- Identity and Breach Monitoring Services: Even with strong defenses, data breaches can expose personal information without any action on your part. Identity monitoring services track whether your email addresses, phone numbers, or credentials appear in known data leaks, giving you early warning to take corrective steps before attackers can act.
Best Practices to Avoid Fake Discount Scams
The practices below offer a practical checklist for evaluating deals and shopping safely online:
How Guardio Protects You From Fake Discount Scams
While awareness and best practices are essential, scam operators are constantly adapting their tactics. Guardio adds a layer of automated, real-time defense that works in the background to catch threats that manual vigilance alone may miss.
- Detects and Blocks Fake Shopping Websites in Real-Time: Guardio evaluates websites as you browse, identifying fake shopping sites based on multiple signals beyond static blocklists. It blocks risky URLs in real-time, including newly created scam domains and deceptive checkout pages, helping stop fraud before you enter payment or account details.
- Prevents Phishing and Credential Theft: Fake discount scams frequently lead to phishing pages designed to harvest login credentials. Guardio identifies these pages and blocks access before any data is submitted, protecting users from the kind of credential theft that leads to account takeovers and follow-up fraud.
- Identifies Malicious Links in Emails, Texts, and Search Results: Scam operators distribute fake discount links across multiple channels, including email, SMS, social media, and search ads. Guardio evaluates links across these entry points, including shortened URLs and multi-step redirects, so that users are warned before they land on a scam page.
- Alerts You to Identity and Data Breach Exposure: Beyond blocking fake stores, Guardio monitors for exposed credentials and data leaks tied to your email addresses and phone numbers. If your information appears in a known breach, Guardio alerts you to take immediate steps, such as changing passwords or enabling stronger authentication, reducing the window of exposure after a scam encounter.
- Stops Scam Attempts Before You Enter Payment Details: The combination of real-time site analysis, phishing detection, and identity monitoring means Guardio can intervene at multiple points in the scam lifecycle. Whether a fake discount reaches you through a social media ad, a search result, or a text message, Guardio is designed to stop it before any payment details or personal information are compromised.
Conclusion
Fake discount scams are among the most common and fastest-growing forms of online fraud. They succeed because they exploit a universal behavior, specifically the desire to find a good deal, and deploy increasingly convincing tactics to make fraudulent offers look legitimate. From inflated pricing and cloned websites to AI-generated storefronts and social media distribution, these scams are designed to bypass casual inspection.
Recognizing the warning signs, such as unrealistic pricing, suspicious URLs, artificial urgency, and unusual payment requirements, is a strong first line of defense. Pairing that awareness with practical steps like cross-checking prices on official sites, using credit cards for traceable payments, and running reverse image searches on unfamiliar products significantly reduces risk.
For shoppers who want protection that works automatically across devices, Guardio combines real-time scam and phishing blocking with identity and breach monitoring to catch threats before they cause harm. Whether a fake discount arrives through a text message, a search ad, or a social media post, Guardio is built to stop it before any damage is done.
{{component-cta-custom}}
FAQs
I run a small business. How do I stop employees from buying supplies from fake discount sites?
Set a clear purchasing workflow so impulse “limited-time deals” don’t turn into fraud losses.
- Require purchases only from approved vendor lists; no new vendors without verification.
- Use virtual company cards with spending limits for online orders.
- Train staff to avoid sponsored search ads and instead type known supplier URLs directly.
- Install real-time browser protection on work devices to block malicious shopping domains.
If you’re tightening your workplace defenses, check out these cybersecurity basics for small businesses.
What’s the fastest way to check if a discount site is a phishing scam?
Pause and verify the site before entering any personal or payment information.
- Search the domain name + “scam” or “reviews” to see if others flagged it.
- Check the domain age using a WHOIS lookup. Brand-new stores are a red flag.
- Look closely at the URL spelling (extra letters, hyphens, odd extensions like .top or .buzz).
- Test the countdown timer. If it resets on refresh, it’s likely fake urgency.
If you’re unsure whether you’ve already clicked something risky, here’s what to do after clicking a phishing link.
Why do fake discount ads keep appearing in my social media feed?
Scammers aggressively target shoppers through paid ads and algorithmic targeting.
- Report suspicious ads directly in the platform to reduce repeat exposure.
- Avoid engaging (even to comment). Interaction signals the algorithm to show you more.
- Clear browsing cookies periodically to reduce ad retargeting.
- Use browser protection that scans links behind social media ads before they open.
Learn more about spotting risky promotions in this breakdown of fake ads on Facebook.
How does Guardio know a new shopping site is dangerous if it just went live?
Guardio doesn’t rely only on static blocklists. It analyzes behavior in real time.
- AI-based detection scans site behavior, not just the domain name.
- Dynamic fingerprinting flags lookalike checkout pages and cloned stores.
- Cross-user threat intelligence blocks scams detected from other users instantly.
- Real-time protection stops the page before payment details are entered.
You can see how this proactive model works in our overview of real-time protection.
Can Guardio protect me from fake discount scams on my phone too?
Yes, Guardio extends protection beyond desktop browsing to your mobile device.
- Enable Mobile Browsing Protection to block malicious shopping sites on your phone.
- Turn on the Text Message Filter (iOS) to stop scam discount texts before you tap them.
- Connect Email Security to flag phishing coupons that slip into your inbox.
- Add your email and phone to identity monitoring to get alerts if your data appears in a breach.
To see where and how you’re protected across devices, visit the guide on where you can use Guardio browsing protection.







