The Brands Scammers Impersonated Most in Q1 2026

Key Takeaways
- Microsoft holds #1 for the second straight quarter, while AT&T jumped from #6 to #2 on the back of fake rewards and service alert texts
- Telekom and USPS entered the top 10 for the first time, riding tax season delivery scams and account verification fraud
- Attackers are mapping campaigns to the calendar: tax deadlines, billing cycles, and product recalls, each triggering targeted phishing waves
- Amazon recall texts, IRS impersonation emails, and Google search ads for "Mac fixes" were the breakout scam tactics of Q1
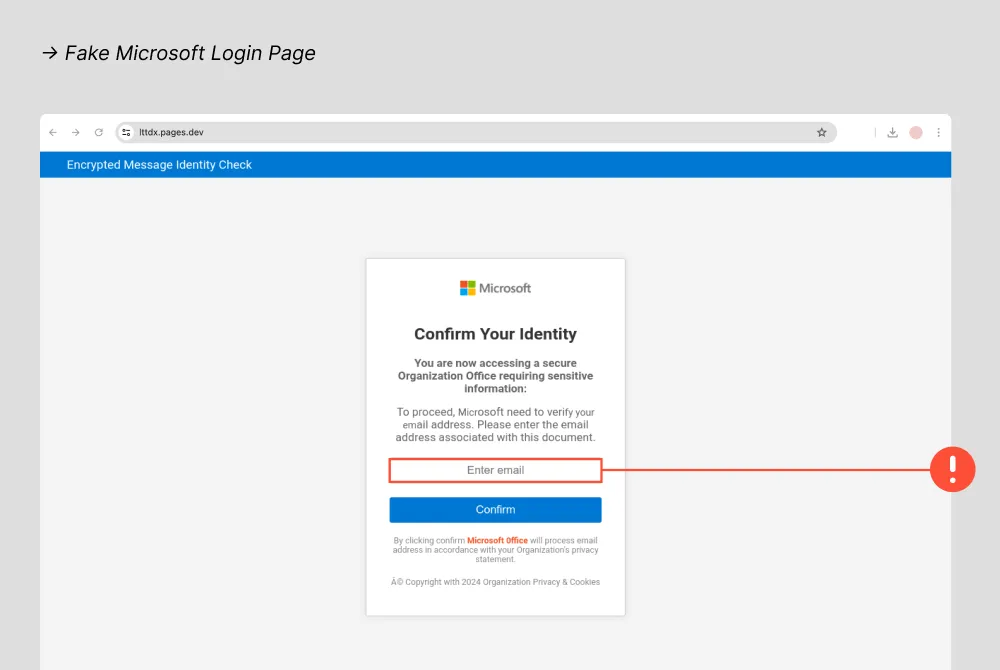
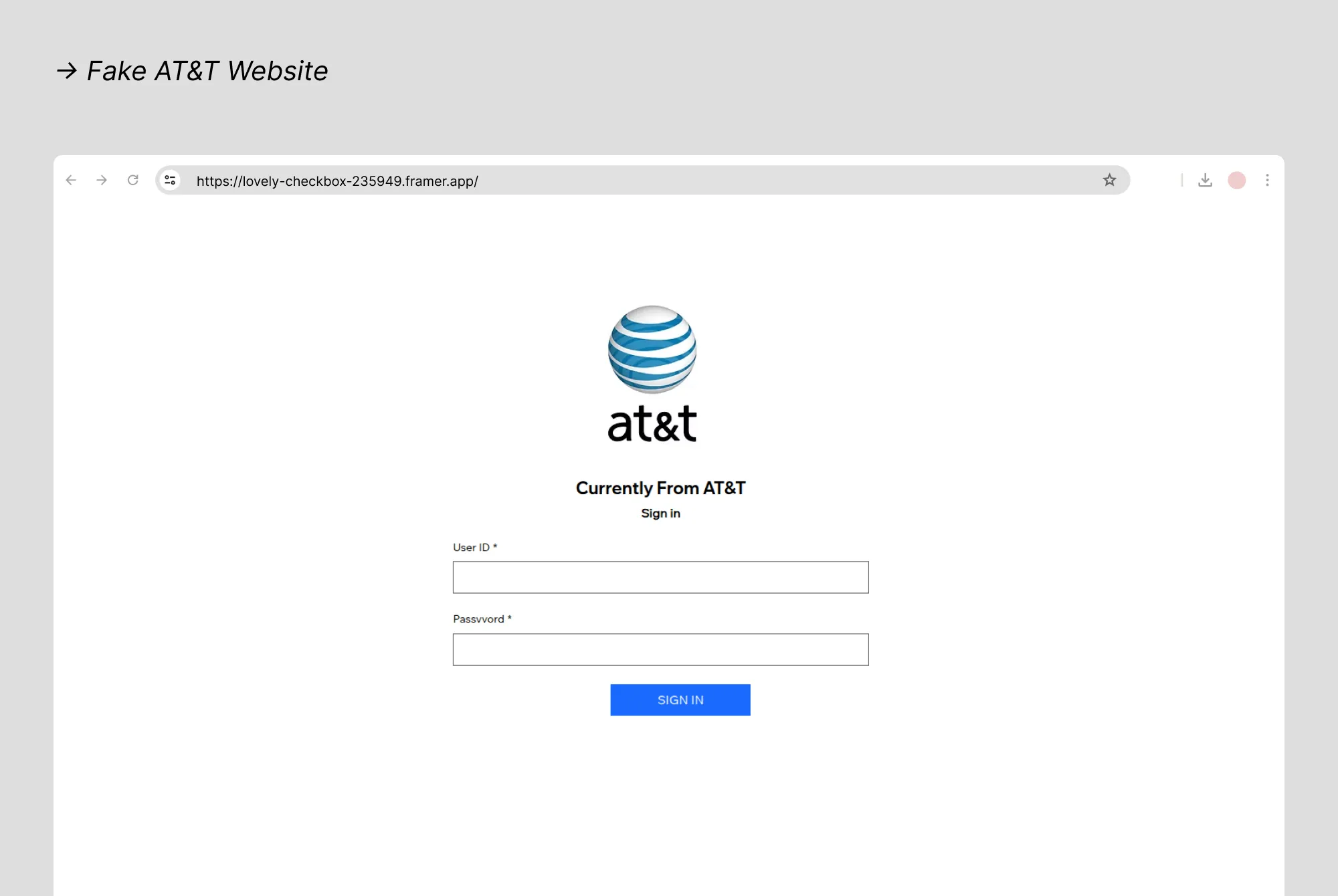
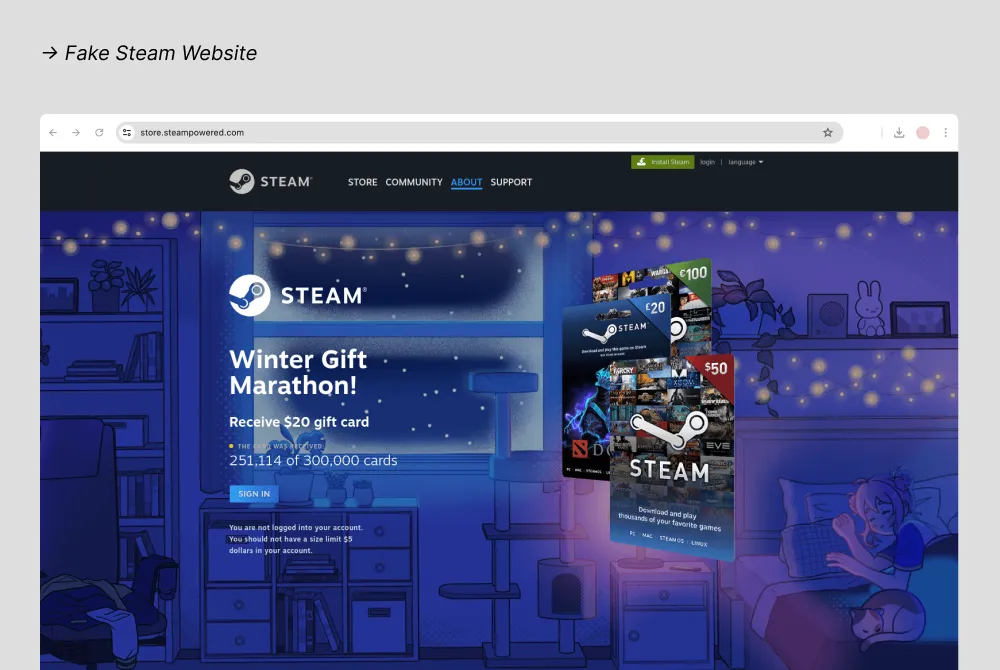
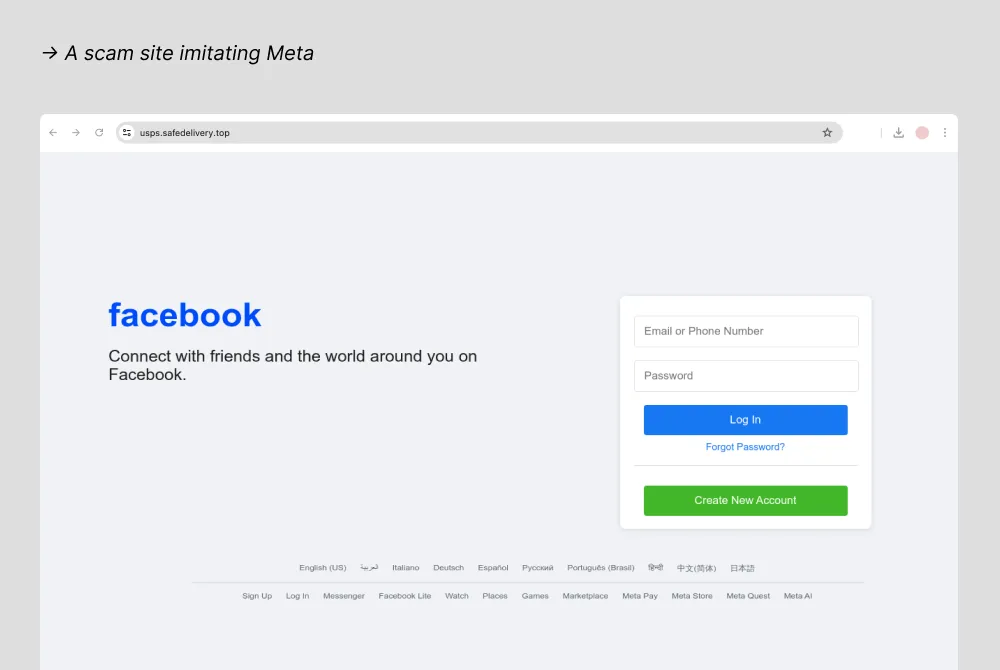
- Fake sites now replicate brand login flows so closely that the URL is often the only giveaway
Scammers are timing their attacks to match your daily routines. Here's who they're impersonating this quarter, how the tactics have shifted, and what you can do right now to protect yourself.
The brands you trust most are the ones scammers wear best.
Q1 2026 brought a shift in how attackers choose their disguises. While holiday shopping scams defined the end of 2025, the first three months of the new year saw phishing campaigns pivot toward tax anxiety, telecom account fraud, and gaming platform exploits. Microsoft held the top spot for the second consecutive quarter, but the bigger story is who climbed the ranks: AT&T surged from sixth to second place as attackers flooded inboxes with fake service alerts and rewards expiration texts, while Telekom and USPS entered the top ten for the first time, riding a wave of delivery scams and account verification fraud that peaked during tax filing season.
Attackers aren't just copying logos anymore; they're mapping their campaigns to the calendar.
January's post-holiday account reviews triggered a fresh round of Microsoft 365 credential theft. February's tax prep rush opened the door for IRS impersonation and fake refund portals. March brought Amazon recall scams timed to coincide with Consumer Product Safety Commission announcements, plus a sophisticated malvertising campaign that hijacked Google search results for "Mac cleaner" queries, redirecting users to fake Apple support pages hosting infostealer malware. Each wave was short, targeted, and designed to match the exact moment consumers were most likely to interact with the impersonated brand, turning routine digital activity into a window of exposure.
With telecom providers, gaming platforms, government services, and cryptocurrency exchanges all represented in this quarter's top ten, the attack surface keeps expanding. The brands we depend on daily remain the masks attackers wear to get past our defenses.
{{component-cta-custom}}
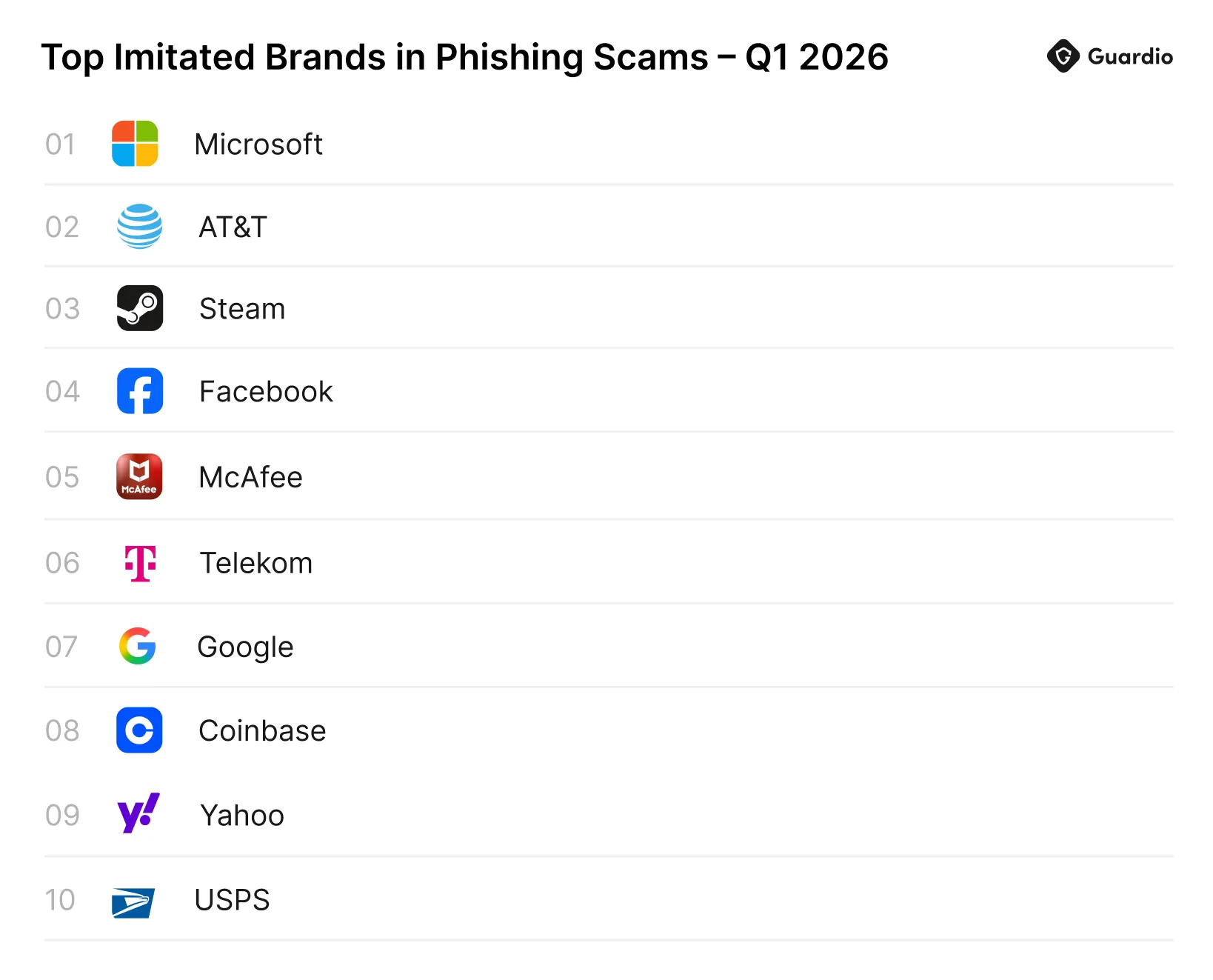
Top 10 Most Imitated Brands in Q1 2026
Here's who made the list this quarter and what changed. The top five stayed familiar, but the bottom half got a shake-up: two brands that weren't on the radar three months ago pushed their way in.
Q1 2026 Most Imitated Brands
- Microsoft
- AT&T
- Steam
- Facebook/Meta
- McAfee
- Telekom
- Coinbase
- Yahoo
- USPS
Every brand on this list grants access to something valuable: credentials, payment methods, personal data, or all three. Microsoft and Google hold work and personal email. AT&T and Telekom control phone accounts tied to two-factor authentication. Steam and Facebook store payment details and social connections. McAfee and Coinbase trade on security and financial trust. Yahoo still manages millions of active inboxes. And USPS sits at the intersection of identity verification and package tracking that people check reflexively during tax season.
The top four brands deserve a closer look because scammers deploy distinct, specialized tactics for each one.
What You Need to Know About the Top 4 Brands
1. Microsoft
Microsoft kept the top spot by riding January's billing cycle. Fake 365 subscription renewal alerts and account security warnings landed in inboxes right when users were expecting legitimate payment confirmations, making them harder to question. The phishing pages capture email, password, and two-factor codes in sequence, giving attackers access to OneDrive, Outlook, and linked enterprise accounts in a single session.
2. AT&T
AT&T jumped from sixth to second on the strength of two SMS campaigns. The first told subscribers their Rewards points were expiring, sending them to a fake AT&T login page that harvested credentials, billing info, and account PINs. The second targeted customers in areas with real service outages, using "service disruption" alerts that were hard to dismiss because they matched something actually happening. Urgency plus plausibility made AT&T the quarter's fastest-rising lure.
3. Steam
Steam stayed in the top three as attackers turned the platform's own social features against its users. Fake gift card pages and Steam Guard verification pop-ups caught people still responding to Winter Sale promotions. But the bigger Q1 tactic was trade offer scams sent from compromised friend accounts, which redirected victims to credential-stealing sites. Each stolen account feeds the next wave: attackers liquidate inventories, sell the account, or use it to scam the victim's friend list.
4. Facebook/Meta
Facebook dropped from second to fourth, but the real shift was how attacks arrived. The lures stayed the same (fake "suspicious login" alerts, policy violation warnings), but delivery moved from email to SMS and WhatsApp. That channel switch caught users who had trained themselves to spot phishing in their inbox but hadn't applied the same scrutiny to text messages. Once an account is compromised, attackers message the victim's entire friend list with investment scams and malicious links, turning one stolen login into dozens of new targets.
Brand impersonation covered the top of the list, but Q1 2026 also produced three standalone scam campaigns worth watching closely.
Fake Amazon Product Recall Texts Are Stealing Account Credentials
Starting in early February, scammers began sending text messages impersonating Amazon, claiming a product from a recent order had been recalled and that the recipient was eligible for a refund. The texts included a link to a fake Amazon page that looked like a standard returns portal. Victims who followed the link were asked to log in and confirm their shipping address and payment details to "process the refund." In reality, the page captured Amazon account credentials, giving attackers access to saved payment methods, order history, and personal information tied to the account.
The campaign gained traction because it aligned with real Consumer Product Safety Commission recall announcements in February and March, making the messages feel timely and plausible. Unlike generic phishing blasts, these texts referenced "your recent order" without specifying a product, a tactic that works because most Amazon customers have ordered something recently enough to second-guess whether the message is real. If you receive a recall notification, go directly to Amazon's website or app and check your order history and the recalls page rather than clicking any link in the message.
Tax Season Scams Surge as the Filing Deadline Approaches
With tax season running through April 15, scammers are exploiting the annual rush by impersonating the IRS, tax preparation services, and state revenue agencies. Phishing emails and texts claim to offer early refund access, warn of filing errors, or threaten penalties for unreported income, pushing recipients toward fake portals that harvest Social Security numbers, banking details, and login credentials for legitimate tax platforms. The IRS flagged these schemes as part of its 2026 Dirty Dozen list, noting that AI-generated messages have made scam communications harder to distinguish from genuine IRS correspondence.
The attacks follow a predictable calendar pattern. January and February bring fake W-2 and 1099 notifications targeting people waiting for tax documents. March sees a spike in fake refund status pages as early filers expect their returns. And as the April 15 deadline approaches, urgency-based scams intensify with threats of audits or penalties for people who haven't filed yet. The IRS will never contact you by text or email to request personal information. If you receive a message claiming to be from the IRS, report it to phishing@irs.gov and verify your filing status through IRS.gov directly.
Scammers Are Hijacking Google Search Results for Mac Fixes
In late January, Guardio's research team uncovered a malvertising campaign that purchased Google search ads for common Mac maintenance queries like "Mac storage full," "clean up Mac," and "Mac running slow." When users clicked these ads, they were redirected through a chain of cloaked URLs to a fake Apple support page that urged them to download a "recommended" cleanup tool. The downloaded software was actually infostealer malware designed to extract saved passwords, browser cookies, cryptocurrency wallet data, and autofill information from the victim's machine.
What made this campaign effective was its positioning. The malicious ads appeared at the top of Google search results, above legitimate tools and Apple's own support pages. Users searching for a fix to a real problem had no reason to suspect that the first result was an attack. The fake support pages used Apple's branding, fonts, and layout patterns, and the download process mimicked what users expect from legitimate Mac software installations. This campaign is a reminder that search results are not guaranteed to be safe. Bookmark official support pages for your devices and navigate to them directly instead of clicking through search ads when troubleshooting issues.
Staying Protected Through Every Quarter
Q1 2026 confirmed a pattern that has been building for over a year: attackers plan their campaigns around the same calendar you follow. Tax deadlines, billing cycles, product recalls, and seasonal promotions all become entry points when scammers can match their timing to yours. Microsoft, AT&T, Steam, and Facebook topped the list not because they are insecure, but because millions of people interact with these brands on autopilot, and that familiarity is exactly what phishing exploits.
Staying safe starts with slowing down. Verify sender addresses before clicking links. Navigate to official websites directly instead of following URLs in messages. Enable two-factor authentication on every account that supports it. And treat urgency in any unsolicited message as a red flag, not a reason to act faster. Scammers count on you reacting before you think.
Manual habits help, but they only work when you catch every attempt. Guardio provides real-time protection that blocks phishing sites, fake login pages, and malicious downloads before they reach you. If your credentials appear in a data breach, Guardio alerts you so you can secure your accounts before attackers use them. Threats don't pause between quarters, and neither should your protection.
Guardio's research team closely monitors phishing scams, identity theft tricks, and emerging online threats, sharing what we learn to help you stay safe.
{{component-cta-custom}}







